3 min read
2 min read
3 Tips to Help Prevent SQL Injections on Your Website
![]() De'Von Carter
Oct 1, 2019 1:08:00 PM
De'Von Carter
Oct 1, 2019 1:08:00 PM
.jpg)
.jpg?width=691&name=iStock-510926380%20(1).jpg)
Before we can explain the specifics of a SQL injection attack, It is important that you understand a basic two tier web application architecture. As stated in the name, there are two parts working together to make your website a reality. The first tier is the web server. The web server can be considered the frontend, or the server that the end users or customers connect to. This is where the pretty pictures and content are hosted and displayed. So, when you go to your favorite website and the page that is presented to you in your web browser (Internet Explorer, Chrome, Firefox, etc…), that is the web server. The second tier is actually holding the really important data on the website.
Website Security Video with CarTek Consulting - How to Prevent SSL Injections
For example, when you go to amazon, the first tier is what you see on the amazon page, but the second tier is holding all of your personally identifiable information (PII), pricing, account information, etc.. and the webserver is pulling that information from the second tier so that it is presented to you as you browse for your next purchase and go to check once you made your production selection. That second tier is called a database. It holds all of the real data that is most important to you. There are many different types of databases, but in this instance, we are focusing on the Structured Query Language (SQL) Database.

Now that we have a better understanding of a two tier web application architecture, let's talk about the actual SQL injection attack. The way these attacks work is fairly simple, but they can wreak havoc for business and website owners. If an attacker wanted to execute a sql injection attack, he/she would go to a page where there is a section that allows for user input. A great example of this is a “contact us” page because there are usually multiple fields that need to be filled out by the end user, customer or in this case the attacker. The attacker would simply type some very specific characters into the fields and those characters would form actual SQL commands that would tell the second tier or database to perform an action. The actions could be to add a user, delete a user, dump the contents of the database, or even delete the entire database. Any of these actions would be very bad for the business/website owner.
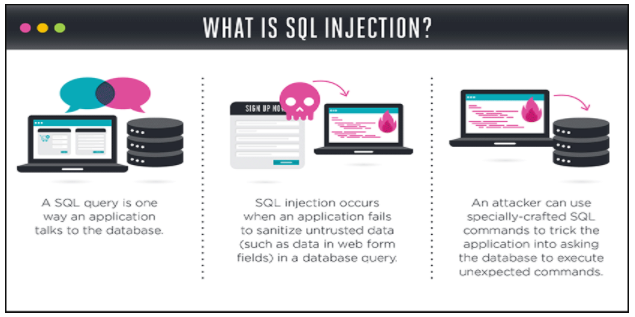 Diagram courtesy of Veracode
Diagram courtesy of Veracode
Now that you see what could happen. Let's turn our focus to some preventative actions that you can take to help protect your business from this type of attack.
- Use an Application Protocol Interface (API) that avoids the use of interpreter tools or have a tool that can provide a parameterized input option.
- Definition of Interpreter - this is a tool that will see executable input that the attacker typed into the contact us page fields and it will perform the action stated in that input. This can be bad.
- Your website should be developed in a way where special characters can be ignored or escaped. This will ensure that when an executable command is put into a field by an attacker, the special characters that are required for the commands to execute will be ignored, thus prevent the command from being run on the database.
- Use a “white list” of user inputs. This means that you implement pre-defined user inputs that could be in the form of a dropdown menu. This will prevent an attacker from having the ability to type in untrusted input.
There are many ways websites are being hacked nowdays. As you can tell from this list, you will need to work with your website developer to implement these preventative measures. If they are a good web developer, they should be familiar with these techniques. If they are not familiar with these techniques, then reach our team of website security experts.

Posts by Tag
- App Development (1)
- B2B (2)
- Build Your Own Website (2)
- Lead Generation (2)
- Local Marketing (3)
- Marketing (11)
- network security (1)
- Non Profit Organizations (1)
- sales (1)
- SEO (8)
- Social Media (1)
- Video Marketing (1)
- web design (9)
- web security (5)
- website maintenance (2)
- website monitoring (3)